
manatee.sh

Bug Bounty: Big Potato Games
oh boy, i went deep diving and here's what i found and received for my holy effortsScene One↑§
It was a cold and windy day, around 8 o' clock in the evening when I saw a post on imgur.com of some amazing dancing skills. It was then I noticed they also posted a link to their company's website [https://bigpotato.co.uk] so obviously I decided to check it out.
I soon realized I've played some of their games and they're actually pretty fun. After I was done looking at their games for some reason I decided just to poke around their website and see what I could find, with no bad intentions, of course.
Back to reality↑§
First thing I done was CTRL + U to view their lovely source and decided to check their filing structure and upon doing so I noticed some open directories with nothing but a few media content and images / assets.
I decided to poke further to see what else I could find.
Next thing? URL Fuzzing to search for any "hidden" directories on their site.
No results apart from their assets folder fortunately.
So I decided to check for any subdomains using pentest-tools.com and that's when I saw a few interesting entries.
To the chase↑§
I found a few subdomains for access to their phpMyAdmin, FTP and SSH. All password protected, obviously. I made no attempts to brute force or anything. There was one last subdomain named "new" so I decided to check that out. I was met with just a basic home page with what seemed to be test data on it, looking like they we're testing out a new framework, Symfony of some kind.
Tried accessing their login page but I was met with many errors and a debug bar, looking at the debug menu and data it was just revealing basic information like their root path and all that jazz. Then I noticed that the profiler has phpInfo() on it too so I opened it up and that little gem listed a lot of information about their whole environment, as you should know.
phpinfo — Outputs information about PHP's configuration
From php.net
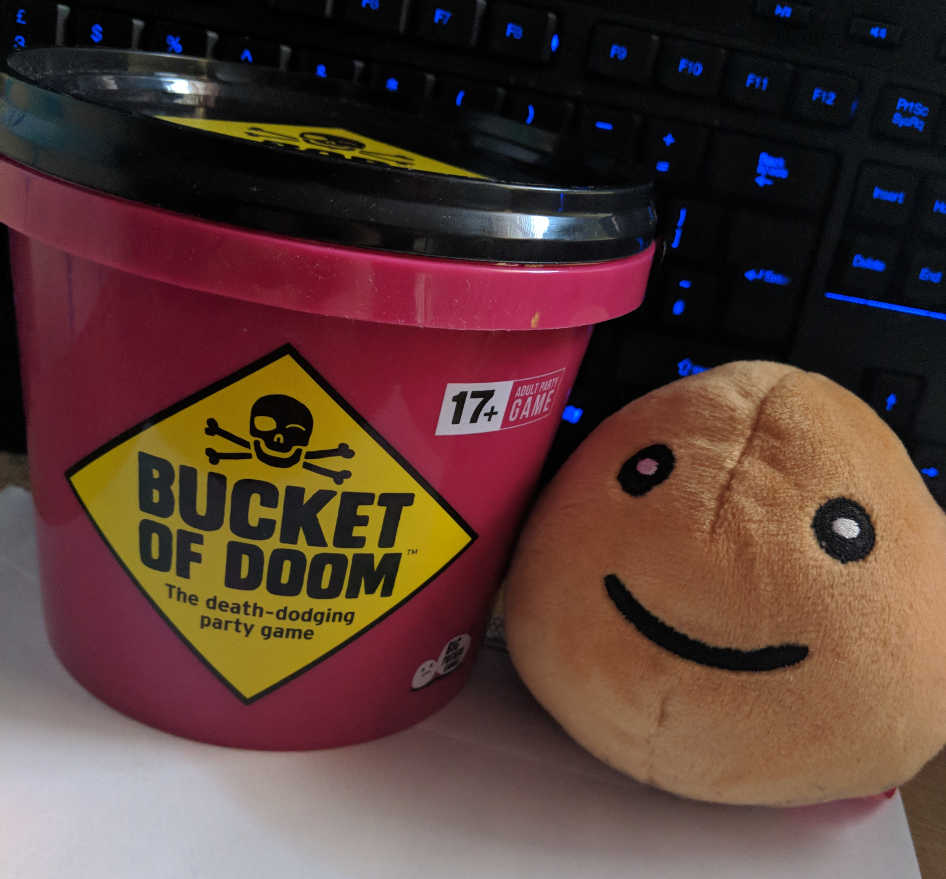
After I found that I decided to send them an email stating what I found, excepting nothing in return. After a day or so a lovely person named Nat got back to my email thanking me and offered me a free game. So sweet isn't it? I chose Bucket of Doom and a week later I had a package arrive with the game and a potato plush.
and just like that, I had my first successful bug bounty, thanks Big Potato.
 :
: